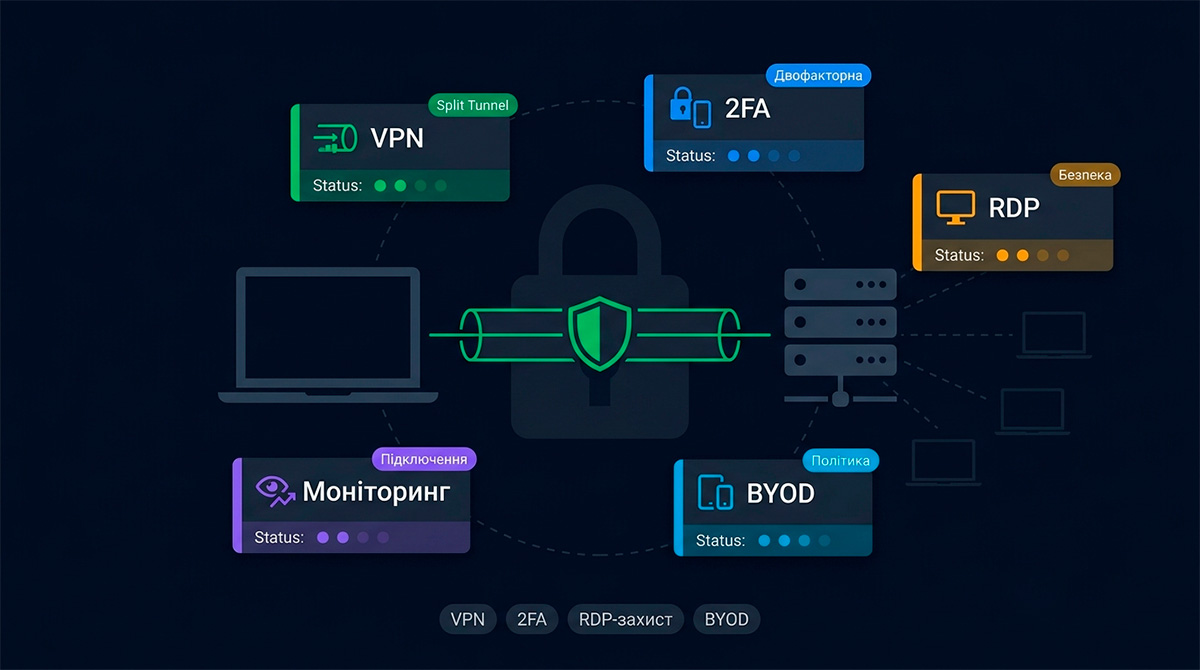
The full-scale war accelerated Ukrainian companies' transition to hybrid and fully remote work. But most companies did this reactively — without proper security infrastructure. The result: corporate data accessible through unsecured home routers, RDP exposed to the internet, passwords shared in Telegram. Let's look at how to do it right.
VPN as the mandatory foundation
Any access to internal company resources — file servers, accounting software, corporate email, IP cameras — must happen exclusively through a VPN tunnel. No "open ports to the outside" for internal services.
Which architecture to choose
Centralized VPN server — the classic scheme. One server (on the office MikroTik or a separate VPS) accepts connections from all employees. Easy to administer, easy to control access. Drawback: if the server is unavailable — all remote access stops.
Mesh VPN (Tailscale, Netbird) — a modern alternative. Each device connects to others directly (peer-to-peer) through an encrypted tunnel. No dedicated VPN server needed, fault-tolerant, ideal for distributed teams. Tailscale for teams up to 100 devices — free.
Split Tunneling: what goes through VPN
Split tunneling defines which traffic goes through the VPN tunnel and which goes directly to the internet. Two approaches:
Full tunnel — all traffic through VPN. Maximum control and security, but overloads the corporate channel with employees' YouTube and Zoom traffic.
Split tunnel — only traffic to internal resources (10.0.0.0/8, 192.168.0.0/16) goes through VPN, the rest goes directly. Optimal for most companies.
Correct split tunnel configuration reduces VPN server load by 70–90% while maintaining full security for internal resource access.
Two-factor authentication (2FA)
VPN with only a username and password is not enough. If an employee's password is compromised (phishing, leak from another service), an attacker gains access to the entire internal network. 2FA is mandatory: TOTP codes (Google Authenticator, Aegis) — free, works offline; hardware keys (YubiKey) — the most reliable option for privileged accounts; push notifications (Duo Security, Microsoft Authenticator) — convenient but requires internet.
RDP security
RDP (Remote Desktop Protocol) is the most popular attack vector on corporate networks. Every day, 4.4 million RDP ports are scanned on the internet. RDP security rules: never expose port 3389 directly to the internet; RDP only through a VPN tunnel; use Network Level Authentication (NLA); limit login attempts (Account Lockout Policy); if access without VPN is needed — RDP Gateway with a certificate.
File sharing
Options for organizing file access for remote teams: Nextcloud self-hosted — full data control, GDPR-compliant, Office integration, mobile clients; SharePoint/OneDrive (Microsoft 365) — simplest if you already have M365; SMB over VPN — classic file shares through the tunnel, simple to configure but poorly suited to slow or unstable connections.
BYOD policy: personal devices at work
BYOD (Bring Your Own Device) is a reality for most Ukrainian companies. Minimum requirements for personal devices connecting to corporate resources: current OS with latest security updates, antivirus software, disk encryption (BitLocker / FileVault), prohibition on saving corporate data to personal cloud storage, ability to remotely wipe the device if lost (MDM solution).
Monitoring remote connections
The administrator must see who connected to the corporate network, when, and from where. Minimum monitoring: VPN server logs retained for at least 90 days, alerts on connections from new countries or unusual hours, automatic disconnection of inactive sessions after N minutes.
Cloud vs On-premise: which is more cost-effective
For companies up to 20 employees: cloud solutions (Microsoft 365, Google Workspace + Tailscale) provide maximum reliability with minimal administration. For companies with 50+ employees and sensitive data: own infrastructure (VPN server + Nextcloud + AD/LDAP) gives full control and often lower cost long-term.
Remote access security is not a one-time configuration but ongoing work. Regularly review access rights, revoke former employees' accounts on their last day, and conduct quarterly VPN configuration audits.